Overview
NAT sessions is the number of open connections a single node behind the router can open to the public network (internet). This is limited by the RAM space allocated for NAT use on the internet gateway.
Supported Devices
ZyWALL 110
ZyWALL 310
ZyWALL 1100
USG40
USG40W
USG60
USG60W
USG110
USG210
USG310
USG1100
USG1900
USG20-VPN
USG20W-VPN
USG2200-VPN
Session Control
Having control over the NAT sessions use can help network professionals guarantee all users a fair amount of sessions for web traffic. By default the Next-Gen firewalls are set to limit the session use to 1000 sessions per user. This number can be increased, lowered or the option can be completely disabled (if necessary). Depending on network size and activity it is a good idea to keep the option enabled to guarantee fair usage.
If you wish to disable the feature there are two ways to go about doing this:
- Uncheck the box "Enable Session Limit" and click the Apply button at the bottom of the screen to save the settings.
- Set the "Default Session per Host" option to '0' (zero, for unlimited) and click the Apply button at the bottom of the screen to save the settings.

Additionally, custom rules can be created based on IP address or user account (only when forced user authentication is enabled). This provides network admins more control over NAT session distribution, for example, the default sessions per host may be limited to 256 while certain users (such as management) may be given 1000 sessions. (depending on Zyxel firewall NAT session capability)
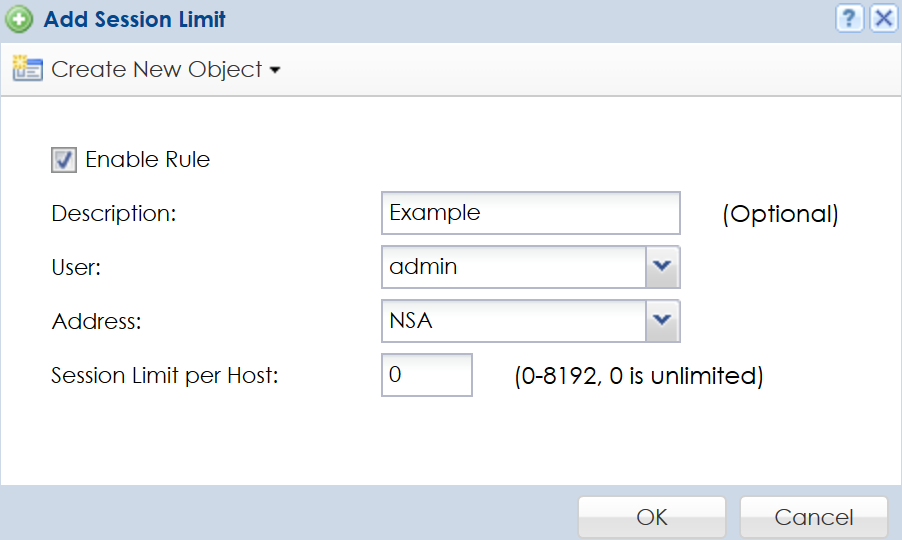
To insert a custom session control policy click the Add button:
- Check the box to "Enable Rule".
- Adding a description is optional, but, this may help to determine what the rule is for in the future when making changes.
- Select the user account or group of user accounts that will be members of the policy. (Note: A user/group account should only be used when web authentication is enabled on the Zyxel firewall for users to be forced to authenticate)
- Select the device ip address or group of ip addresses that will be members of the policy.
- Specify the "Session Limit per Host" for the policy.
- Click OK to save the settings.
Comments
0 comments
Please sign in to leave a comment.