This guide will assist in the configuration of the ShrewSoft VPN Client (version 2.2.2) for VPN connectivity with Zyxel's Next-Gen ZyWALL USG routers.
Overview
A VPN (virtual private network) provides a secure communication between sites without the expense of leased lines. VPNs are used to transport traffic over the internet of any insecure network that uses TCP/IP communications. A remote access VPN (client-to-site) allows employees who are traveling or teleworkers, secure access to company network resources. There multiple types of VPN protocols/technologies, that can be used to establish a secure link to company network, L2TP, PPTP, SSL, OpenVPN, etc.. This guide will reference the IPSec protocol to establish a secure VPN tunnel between external hosts (users connected to the internet outside the company network structure) and the ZyWALL router. Third party IPSec software is required to establish the VPN connection as current operating systems lack a built-in IPSec client. This walkthrough will help configure the VPN setup on the ShrewSoft VPN client (version 2.2.2).
Supported Devices
ZyWALL 110
ZyWALL 310
ZyWALL 1100
USG40/40W/40HE
USG60/60W
USG110
USG210
USG310
USG1100
USG1900
USG20-VPN/20W-VPN
USG2200-VPN
ZyWALL VPN Setup
To begin the configuration of the VPN policy on the ZyWALL/USG router, please open a web browser and access the Zyxel routers WebGUI. Once in the web configuration page go to menu, Configuration → VPN → IPSec VPN to begin the VPN policy/rule setup.
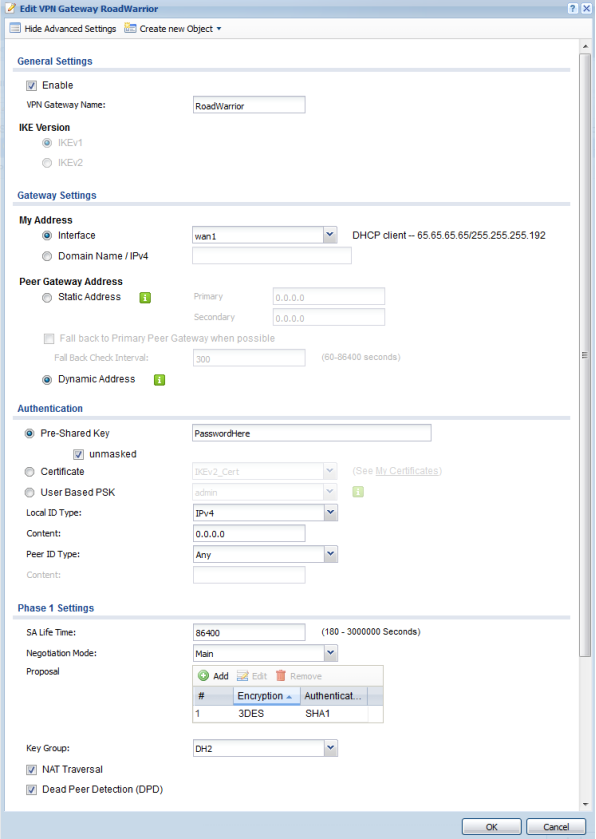
VPN Gateway (Phase 1):
In the IPSec VPN menu click the "VPN Gateway" tab to insert a Phase 1 VPN policy configuration. Click the "Add" button to create a new rule. On the top left of the window click the "Show Advanced Settings" button to view all the option available in this menu.
- Check the box to enable the VPN rule
- VPN Gateway Name – Please provide a name for the rule
- IKE Version – Options are IKEv1 and IKEv2, select the appropriate IKE version you wish to use. This will depend on your VPN clients compatibility, not all clients support IKEv2. Verify support with the software manufacturer before creating the rule on the Zyxel router.
- My Address – Select the WAN interface you wish to use to establish the VPN connection under the "Interface" dropdown field or select "Domain Name/IPv4" to manually enter a domain name/DDNS name or IP address.
- Peer Gateway Address – Select the "Dynamic Address" bullet to allow VPN connection from any public IP. This is required to be able to establish a VPN connection between VPN software and the VPN router.
- Authentication – Select "Pre-Shared Key" and enter a password for the VPN tunnel. You can also use a certificate to establish the VPN connection. The VPN software client must support certificate based authentication policy. If using certificate to establish connection do not forget to export the cert from the Zyxel router and import into the VPN software client.
- Phase 1 Setting – Choose the desired Negotiation Mode, Encryption, Authentication and Key Group algorithms you wish to use (Negotiation Mode option are Main and Aggressive) (Encryption options are DES, 3DES, AES128, AES192, AES256) (Authentication options are MD5, SHA1, SHA256, SHA512) (Diffie-Hellman key group options are DH1, DH2, DH5)
- Click "OK" to save the settings.
Note: The caution symbol to the right will appear on areas where input is required or if there is a mistake with the entry, such as illegal/unsupported characters.
VPN Connection (Phase 2):
Click on the "VPN Connection" tab to create the Phase 2 portion of the VPN tunnel. Click the "Add" button to insert a new rule. On the top left of the window click the "Show Advance Setting" button to view all available options in this menu.
- Check the box to enable the VPN rule
- Connection Name – Please provide a name for the rule
- Set the VPN Gateway application scenario to use "Remote Access (Server Role)"
- On the application scenario set the VPN Gateway dropdown to use the Phase 1 policy that was created on the previous step. (RoadWarrior for this example)
- Policy – Set the Local Policy to use the "LAN1_SUBNET" address object, this will give the VPN user access over all devices connected to LAN1
- Phase 2 Setting – Choose the desired Encapsulation, Encryption and Authentication algorithms you wish to use (Encapsulation option are ESP and AH) (Encryption options are DES, 3DES, AES128, AES192, AES256, NULL) (Authentication options are MD5, SHA1, SHA256, SHA512)
- Perfect Forward Secrecy (PFS) – Is an added level of encryption, it is not necessary to enable it, but, if you wish to use the added encryption level the options are None, DH1, DH2 and/or DH5
- Related Settings – make sure the Zone is set for "IPSec_VPN"
- Click "OK" to save the settings.

ShrewSoft VPN Client Setup
The ShrewSoft IPSec VPN Client is a free VPN application for Windows, BSD and Linux computers. You can download a copy of the client from here. Because the client is not manufactured or engineered by Zyxel we do not offer technical support for the client. Any issues related to the software need to be brought to the attentions of Shrew Soft Inc.
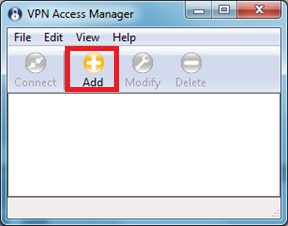
To configure the VPN client based on the ZyWALL setup example above, please open the "VPN Access Manager" from Shrew Soft. On the application please click the "Add" button to create a VPN site configuration policy.
On the clients "General" tab make the following changes to the setup:
- Remote Host – Type in the domain name/DDNS hostname or public IP address of the VPN router.
- Port – The VPN port the Zyxel router uses is UDP:500, this is the standard IKE port.
- Auto Configuration – Options for this field are: disabled, ike config pull, ike config push and dhcp over ipsec. This option must be set to disabled, the ZyWALL/USG routers do not support any of the auto configuration options the ShrewSoft VPN Client has to offer.
- Local Host – Set the Adapter Mode to "Use an existing adapter and current address"

Click the "Client" tab and make the following changes to the setup:
- Firewall Options – Set the NAT Traversal setting based on what was configured on the Zyxel router, in most cases NAT Traversal is not needed. IKE Fragmentation should be disabled, this option is not needed.
- Other Options – Enable Dead Peer Detection will automatically send an "Are You There" packet to confirm the VPN connection is still active, this will not work if the Zyxel/USG router does not support the function or is not enabled. Enable ISAKMP Failure Notifications logs failed connection attempts by the software client, not really needed to establish a VPN connection but will not hurt if enabled.

Click the "Name Resolution" tab and make the following changes to the setup:
- DNS – Enabling DNS through the tunnel is not necessary if the tunnel is only used to access network resources.
- WINS – Enabling WINS for the tunnel will help resolve computer hostnames to their corresponding IP address on the network.

Click the "Authentication" tab and make the following changes to the setup:
- Authentication Method – Options are Hybrid RSA + Xauth, Hybrid GRP + Xauth, Mutual RSA + Xauth, Mutual PSK + Xauth, Mutual RSA and Mutual PSK. Set the option to Mutual PSK based on example ZyWALL/USG VPN rule created above.
- Local Identification – Leave the setup as is (based on example ZyWALL/USG VPN setup)
- Use a discovered local host address option should be checked

- Remote Identification – Leave the setup as is (based on example ZyWALL/USG VPN setup)
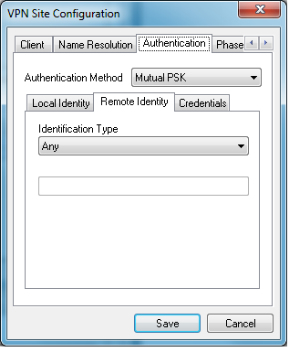
- Credentials – Type in the "Pre-Shared Key" to match the one created on the ZyWALL/USG VPN setup example.

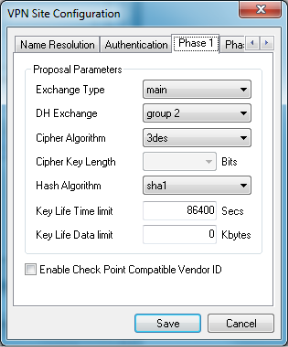
Click the "Phase 1" tab and make the following changes to the setup based on the ZyWALL/USG VPN setup:
- Exchange Type – Main
- DH Exchange – Group 2
- Cipher Algorithm – 3DES
- Hash Algorithm – SHA1
- Key Life Time Limit – 86400
- Key Life Data Limit – 0
- Enable Check Point Compatible Vendor ID should be unchecked
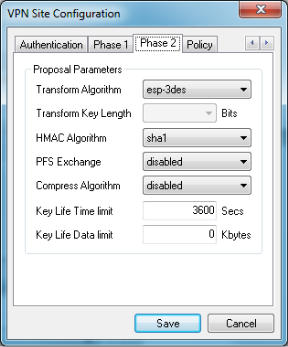
Click the "Phase 2" tab and make the following changes to the setup based on the ZyWALL/USG VPN setup:
- Transform Algorithm – ESP-3DES
- HMAC Algorithm – SHA1
- PFS Exchange – Disabled
- Compress Algorithm – Disabled
- Key Life Time Limit – 3600 (max 28800, this is a limitation on the ShrewSoft VPN Client software)
- Key Life Data Limit - 0
Click the "Policy" tab and make the following changes to the setup:
- Policy Generation Level – Options are auto, require, unique and shared. Select "require" for this option.
- Maintain Persistent Security Association should be disabled
- Obtain Topology Automatically or Tunnel All should be disabled
- Click the "Add" button to insert a remote network resource entry

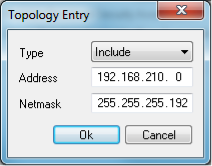
Based on the ZyWALL/USG VPN setup the rule allows VPN connected users access over the LAN1_SUBNET. This network has an IP scheme of 192.168.210.0/26 or 192.168.210.0/255.255.255.192. On the "Topology Entry" do the following:
- Type – Select "Include"
- Address – Type in 192.168.210.0
- Netmask – Type in 255.255.255.192
- Click the "OK" button to add the remote network resource entry
Click the "Save" button to apply the settings and create the IPSec VPN dialer.

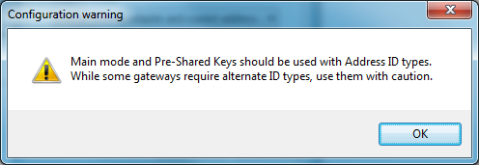
You main get a warning like the screenshot below when saving the settings. Click the "OK" button to continue with the save process.
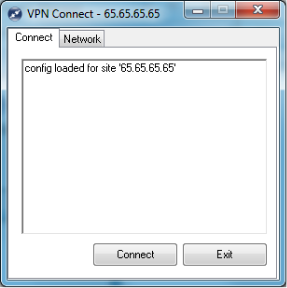
Once the VPN dialer is created, click to highlight the connection dialer and press the "Connect" button to open the connection dialer.
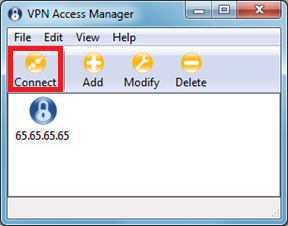
Within the connection dialer you have the option to Connect the tunnel or Exit the dialer. Click the "Connect" button to begin the IPSec VPN connection.
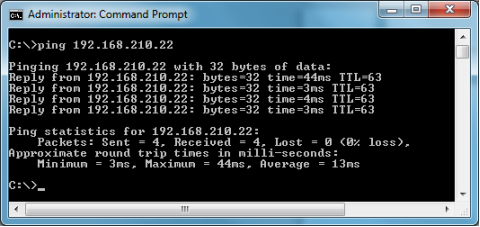
Once the tunnel is established open a command prompt window (Windows OS) or terminal window (Linux OS) and attempt to ping a device across the VPN tunnel to verify traffic is passing through.
Note: Make sure the device you are pinging is set to respond to ICMP/PING requests.
Comments
0 comments
Please sign in to leave a comment.